Once this can be made to work on a mass deployment scale and the drawbacks are overcome, it might just be the ticket to ride for objects of the IoT/E, CoT.

Quantum cryptography (QC for this discussion) theory—and it is still just theory—is potentially a very powerful security process that could be implemented for the dissemination of information over communications channels, using the principles of quantum mechanics. This is particularly intriguing because it is impossible to measure a photon, the fundamental element in the creation of QC secure keys, without affecting its behavior.
“Quantum cryptography relies on the principle that anything which is being observed changes,” said Roel Schouwenberg, principal security researcher, of Kaspersky Labs. “This means it is impossible to intercept/wiretap the traffic between two nodes, as intercepting the data would mean changing it. Therefore, quantum cryptography is unbreakable under the current law of physics when implemented well.”
QC is being eyed as a methodology able to efficiently generate an unbreakable secure key that can be used to protect sensitive data. By using elementary particles—in this case photons—QC can generate keys to establish confidential communications. It can also, with near foolproof certainty, alert the users if the key has been compromised.
There is a cautious underpinning of excitement about how QC could revolutionize the IoT/E, CoT by enabling worry-free, unimpeachable connections between its objects. If that were to become reality, the single, most looming concern of the IoT/E, CoT will have come to pass. And that would open the gates to truly un-bridled, and unprecedented developmental arenas that would create the all-is-connected-to-everything final frontier of the IoT/E, CoT.
Reality check
Just because it isn’t ready for prime time doesn’t mean it isn’t worth a discussion. Quantum physics is fascinating, and the collective quantum theory has been around for more than 100 years. The first attempt to explain it was a bit lateral to how we see it today. It was proposed by Professor Max Planck, who coined the term “quanta” (the early term for photon), the base from which quantum physics evolved.
Over the years, significant contributions and modifications from the likes of Bohr, Einstein, Werner, Dirac, Born, Heisenberg, Pauli, and von Neumann have shaped it to how we define it today. But the basic premise holds true. For example, if it wasn’t valid, devices such as transistors wouldn’t be able to work. In addition, there has been some success with quantum mechanics near absolute zero, but somehow that doesn’t seem practical for QC. And QC is still in early stages of the theoretical roadmap.
The theory of QC
QC is a point-to-point (P2P) lightwave-based transmission technology that uses photons via a fiber optic cable link. Benjamin Jun, CTO of Rambus’ Cryptography Research Division, explains why it is such an ideal medium for the next level in secure communications: “For one thing, the transmissions can be audited, and the physics of quantum mechanical effects can be applied to determine if any eavesdropping occurred. One way of doing this is via quantum key distribution. This process first inspects for transmission integrity, then transmits random keys via the quantum cryptography mechanism. Conventional cryptography is then used to secure subsequent communications.”
This seems like the ideal solution for the IoT/E, CoT. By far, the looming concern with the IoT/E, CoT is how to secure what are likely to be millions of low-end chip objects that are totally autonomous. It doesn’t solve the direct chip access issues such as side channel attacks, but it does suggest an almost foolproof platform for securing the communication channel that all IoT/E, CoT objects use to interconnect. Being able to inspect such things as keys and unequivocally, know that have been compromised or not, is invaluable.
But how does a photon become a key? And information attached to a photon’s spin so it can be used to create binary data? The theory is actually relatively simple. It involves the state of the photon and filters on both ends of the link.
A photon has the ability to be polarized, and that is the magic bullet. Photons can be polarized to one of four angular states: 0º, 45º, 90º, and 135º. The zero and 90º polarizations are called the rectilinear basis, the 45º and 135º polarizations are referred to as the diagonal basis (see Figure 1.)

Figure 1. Graphical representation of polarization and basis.
At the transmitting end, the photons are sent through a polarization filter and are transmitted in one of the four angular states. At the receiving end, the photons’ polarization is measured with either a rectilinear or a diagonal filter. The filter is chosen on a random basis, and the result is cataloged. The type of the measurement (rectilinear or basis) only, is returned to the sender. The results the actual angle of the photon (remember, each type has two angular possibilities) remains unknown to the sender.
The next process verifies which of the transmitted and received photons match in angular states. The matches are kept, the mismatches discarded. The retained photons are then translated into 0’s and 1’s to create a secure key. Figure 2 is a graphical illustration of the process.
This is accomplished through a communication between the sender and receiver where each state is simply verified as correct or incorrect. Anyone eavesdropping will only be able to discern that the photon is one of two angular possibilities, not one of four.
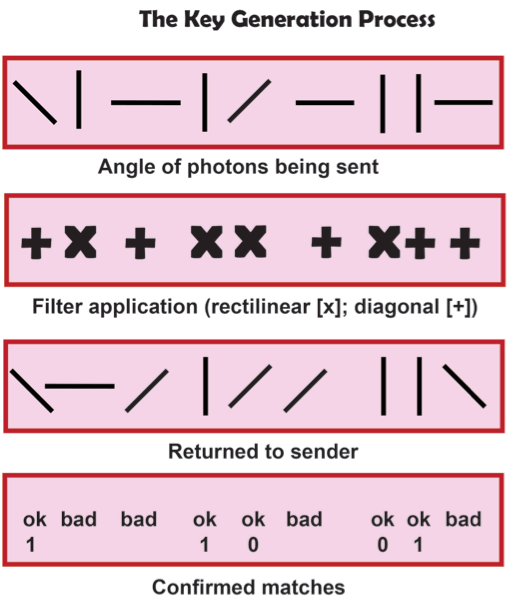
Figure 2. Graphical representation of the key generation steps.
Once the key is in place, as long as no attempt is made to intercept the photons, the key will remain secure as it continues to precede each transmission. As has been noted earlier, any attempt to measure or “look” at photons would result in a change in their state. A monitoring network, of some sort, is implemented in the transmission path to detect whether there has been a state change in any of the photons during transmission. If it detects any tampering, it can break the link, and notify the parties that an attempt has been made to compromise the link.
Problems to solve
Despite all that QC has on the upside, there are some downsides – in both deployment, and impermeability. So as positive as it seems, and while some consider it the ultimate secure key link, there are still challenges that have to be overcome.
“There are significant drawbacks to using quantum cryptography in real-world situations,” Jun notes. “Messages must be sent point-to-point, and they cannot be Internet routed. They also cannot use Wi-Fi communication, and there is no cost-effective way to deploy the technology through the ‘last mile.’ While limited solutions have been on the market for 10 years, quantum cryptography is not used on any commercial scale.”
Chief among the roadblocks is the distance light can travel without attenuation; it’s short when compared to other methods such as cable and microwave. In addition, photons can have their spin altered by other particles as they travel along the cable. Thus, when it reaches the destination, it may no longer have the angle of origination. There is also the simple loss of intensity (attenuation) as it travels down the cable, as well as the phenomenon known as “scattering” (photons reflecting off of the, however slight, molecular imperfections of the glass).”
A short primer on entanglement
As was touched upon earlier, there is a phenomenon that occurs in photonics known as “entanglement.” Though not extremely well understood, enough is known about it that it can be theorized in QC to increase link distance and improve tamper resistance (there is also an element of entanglement that makes it vulnerable to eavesdropping).
Globally, entanglement theory makes the impossible, possible. Two of the more referenced applications are quantum teleportation and super dense coding. But in this case entanglement implies that when two particles are entangled, if the properties of one particle are known, so are the properties of the other—instantaneously. This is based upon one of the fundamental precept of quantum physics, that particles possess the same properties when entangled, regardless of distance between them.
In theory, observable properties of any given pair of photons can be entangled. The qualifier is that the correct form of the entangled state between the two photons must exist to define the observable. This can be proven by the following:
Assume two identical particles (in this case photons), whose states are described by the Hilbert space H. Assign Ω to be the observable, of which two selected, normalized eigenvectors |ω1⟩ and |ω2⟩, with corresponding eigenvalues ω1 and ω2, are defined. The observable can, in principle, be any desired element such as angular momentum, position, spin, polarization, etc.
Given the above, the state of the combined two photons exists as:
|ψ⟩=1/√2(|ω1⟩|ω2⟩+|ω2⟩|ω1⟩)
Therefore, this state equation proposes that, if the observable is derived on one of the photons and the result is ω1, then the result of any simultaneous measurement of the observable on the other photon will produce ω2. This also works in reverse (ω2 to ω1).
What this means to QC is that when a sequence of correlated particle pairs is generated, one member of each pair will be detected by each party. If there was an eavesdropper on this communication, they would have to detect a particle to read the signal, and retransmit it in order for his presence to remain unknown. However, the act of detection of one particle of a pair destroys its quantum correlation with the other, and the two parties can easily verify whether this has been done, without revealing the results of their own measurements.1
Putting it into perspective
QC has been successfully accomplished in a laboratory setting, but, as Jun noted, there are no commercial installations as of today. It sounds great on paper and in theory. However, much of it is just that – theory.
Today the process requires very large and expensive lasers. The trick will be to scale it down to the IC level, and implement it utilizing standard silicon processes. That will open a floodgate of progress in the field and be the enabler that will make it mainstream. Unfortunately, there is no timetable for that happening yet.
There are also some potential vectors where entanglement can be used to crack QC transmissions. In an experiment at MIT, researchers were able to back-door the entanglement process by actually entangling two separate intercepted photons. By measuring the properties of one of them, they were able to guess the identical property on the other one, without any observations on it, or changing it. The second one can be sent on its way, none the wiser and yet its state was observed. While this was an experimental process, if it can be perfected, and applied in a linear fashion to strings of photons, it may offer a way to compromise the “unbreakable” QC key, and other quantum transmissions. So again, as is so often the case, security may only be one step ahead of the hacker.
There is a fair amount of data available that discusses QC, and all of the related theory and progress. But a lot needs to be done before we can use it for practical application. But we should hurry. The IoT/E, CoT isn’t that far away.
Leave a Reply